Leveraging Splunk for Palo Alto Firewall Logs – Part 1
Palo Alto Networks‘ products offer unparalleled visibility into network traffic and malicious behavior, spanning across both network and endpoint environments. Integrating this visibility with Splunk enables us to correlate data and conduct analytics across various data types.
Prerequisite
- A working instance of splunk server
- A valid account on splunk.com (to download the needed app)
- Palo Alto Networks Firewall
Configuring Splunk
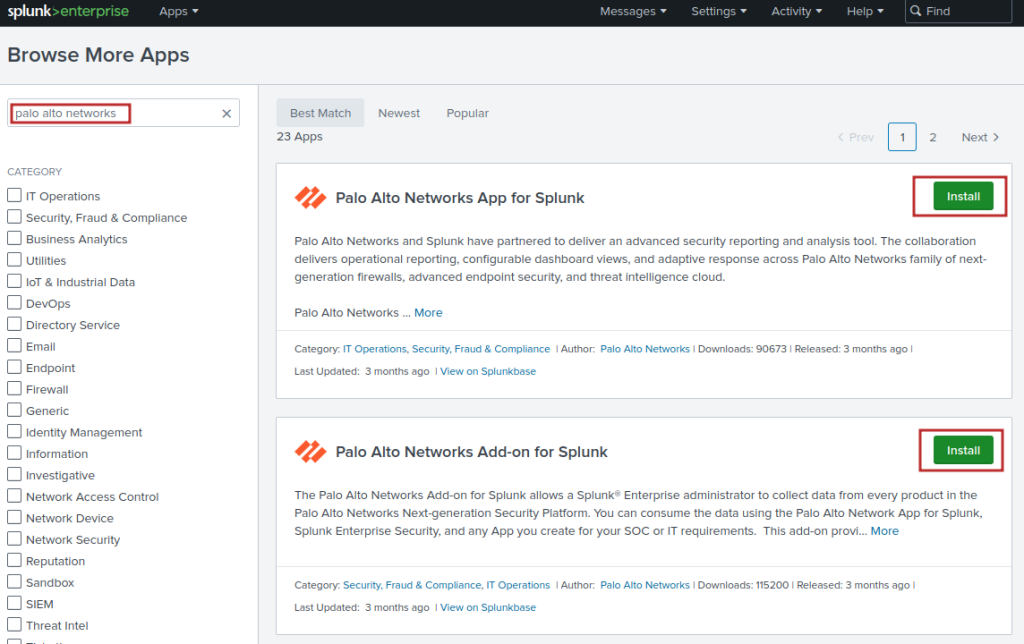
We need to first install the two apps from the splunkbase repository. You need an active account (Free) in order to download the app:
Enabling Data Model Acceleration
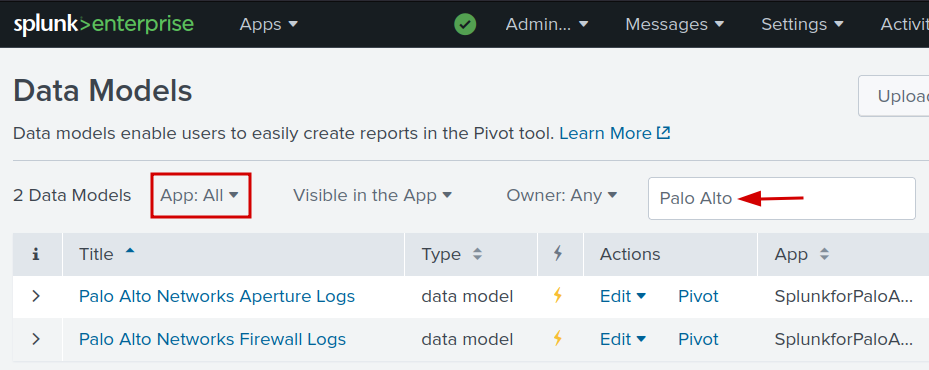
- Navigate to Settings -> Datamodels
- Select All in the App dropdown box
- Enter Palo Alto in the filter field
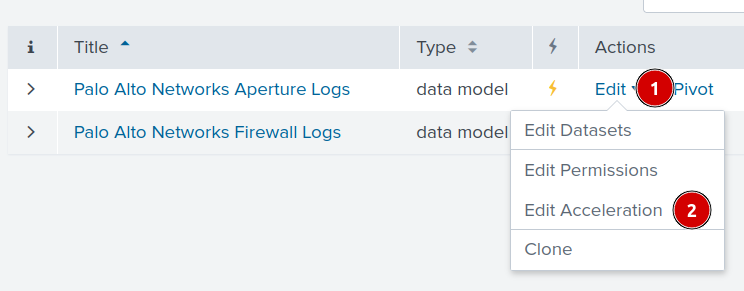
You will need to repeat the steps below for both Palo Alto Networks Aperture Logs and Palo Networks Firewall Logs in order to enable data model acceleration
- Click on Edit -> Edit Acceleration
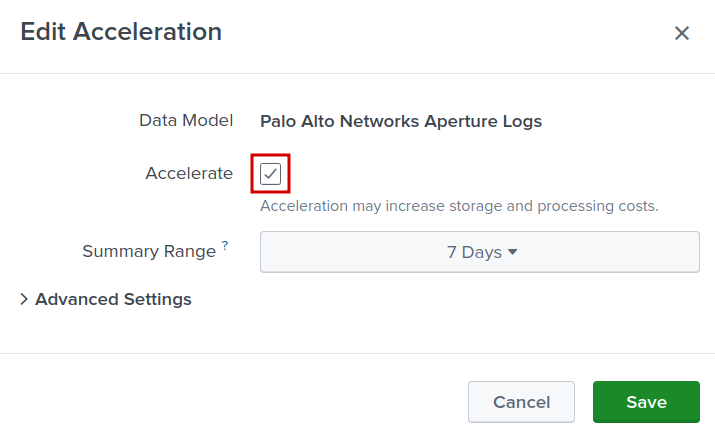
- Check Accelerate
- Click Save
Setting up Data input
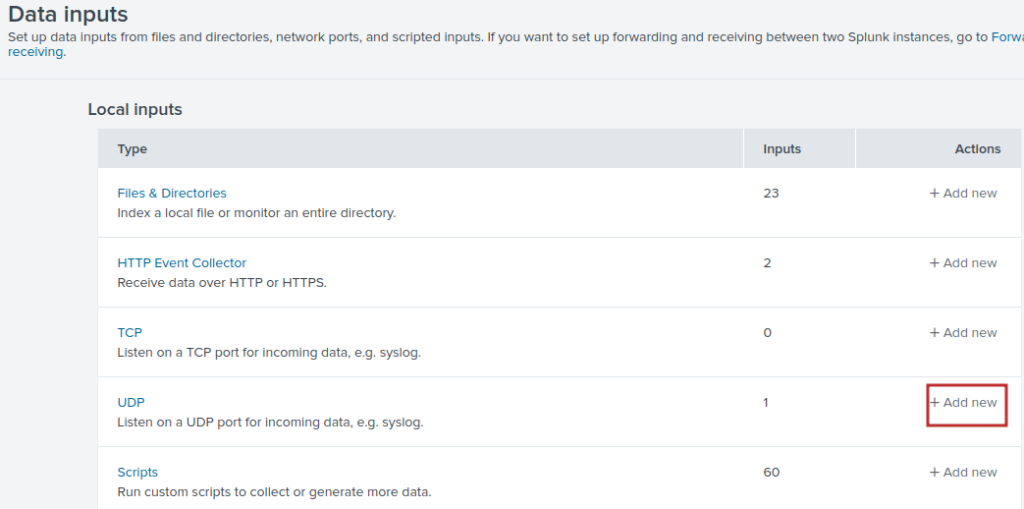
- Navigate to Settings -> Data Input
- Click on Add new actions for the UDP Protocol
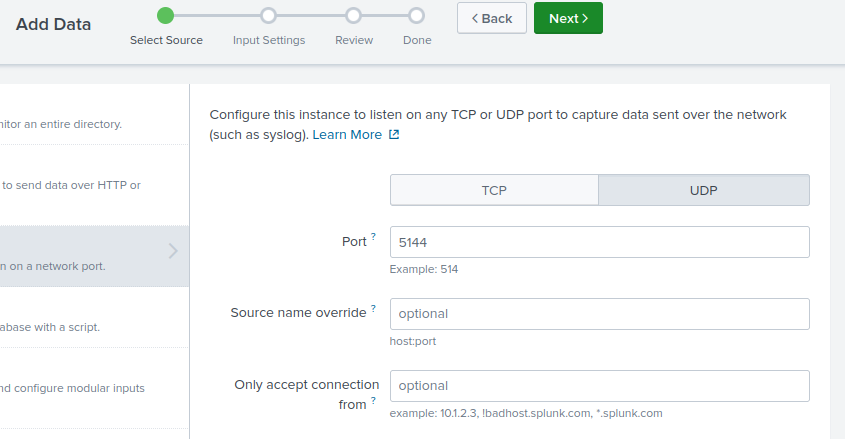
- Input the port number: 5144
- Click Next
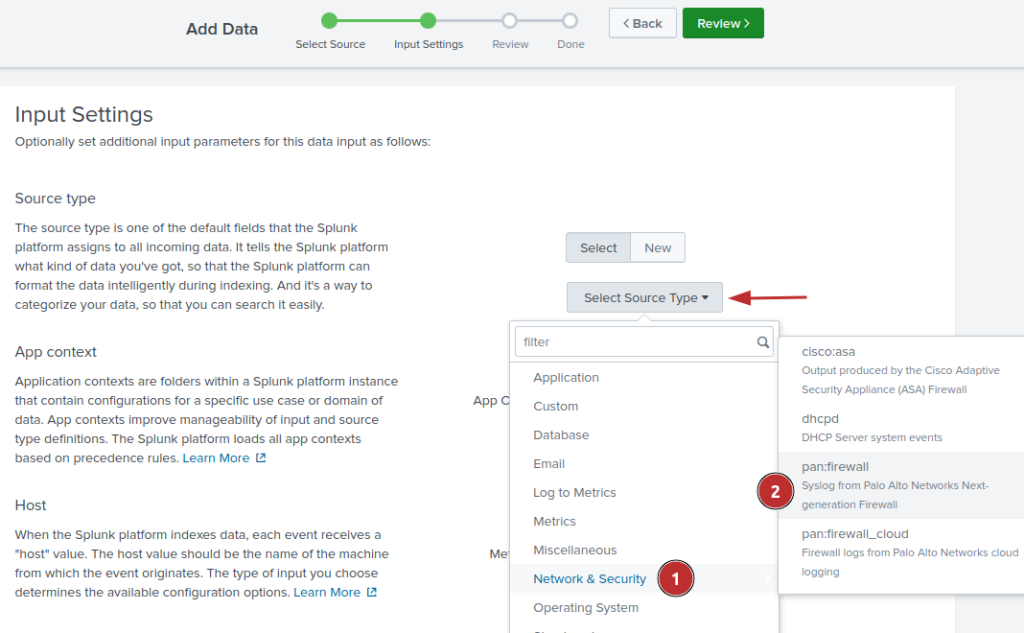
- Click Select Source Type -> Network & Security -> pan:firewall
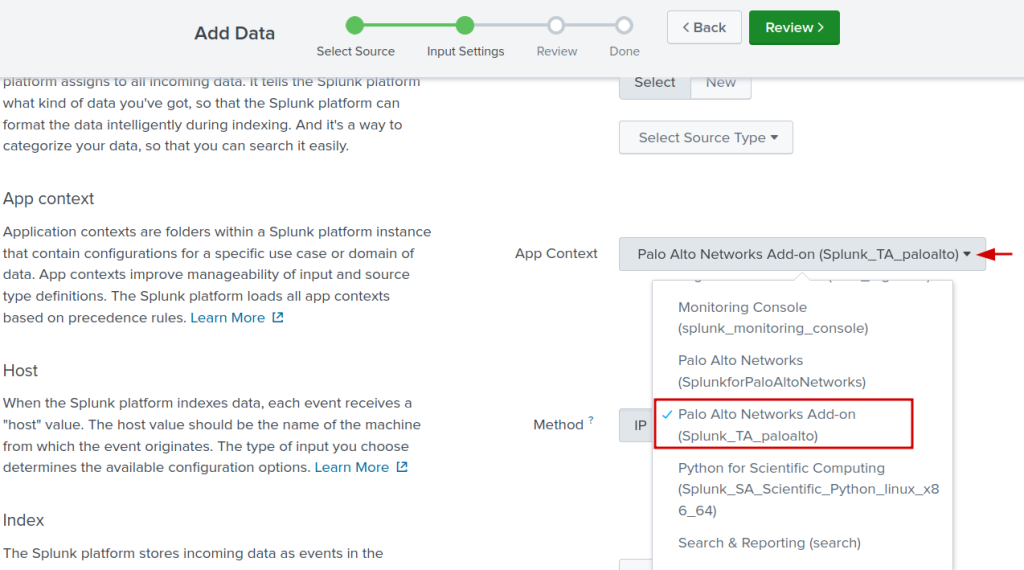
- Change the App Context to Palo Alto Networks Add-on
- In the index section, click on create new index and we are going to name it paloaltonetworks
- Click on Review
- Cick on Submit to finish
Configuring Palo Alto Networks Firewall
We will be using the PA-VM series NGFW for the purpose of illustration throughout this blog post.
By default the firewall will use the management interface for all of its service routes, unless additional configuration is made to use a different interface.
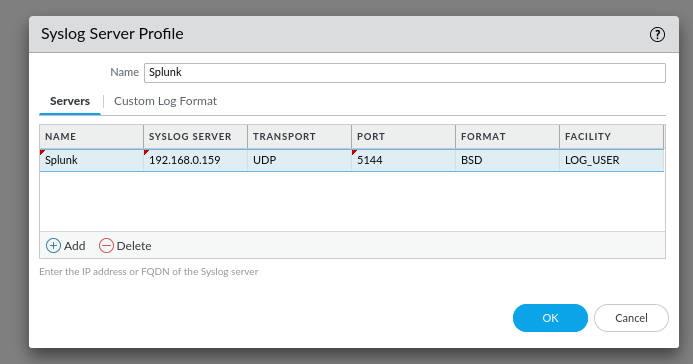
Syslog Server Profile
We will need to setup a Syslog Server Profile in the configuration.
- Device -> Server Profiles -> Syslog
- Click on Add to add a new profile
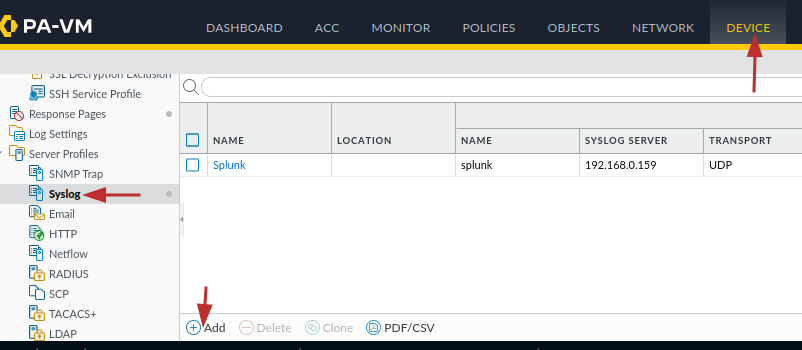
- Add the name, IP Address or FQDN of your splunk server. Adjust the protocol and port as needed
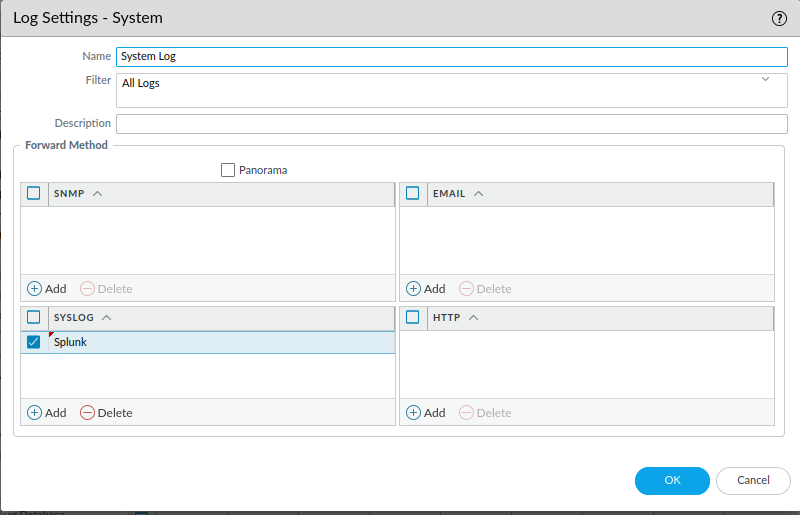
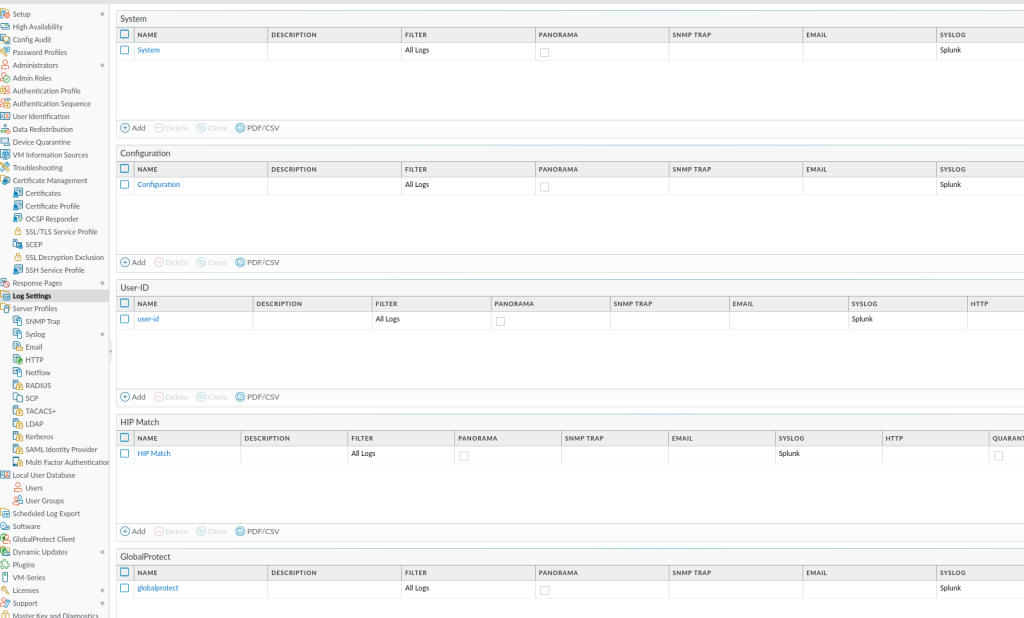
Log Settings
In order to forward logs like system, configuration (firewall changes), User-ID, GlobalProtect, we will need to specify a Syslog profile for each category of the log. We will use the previously created Syslog Server Profile named “Splunk“.
- Navigate to Device -> Log Settings
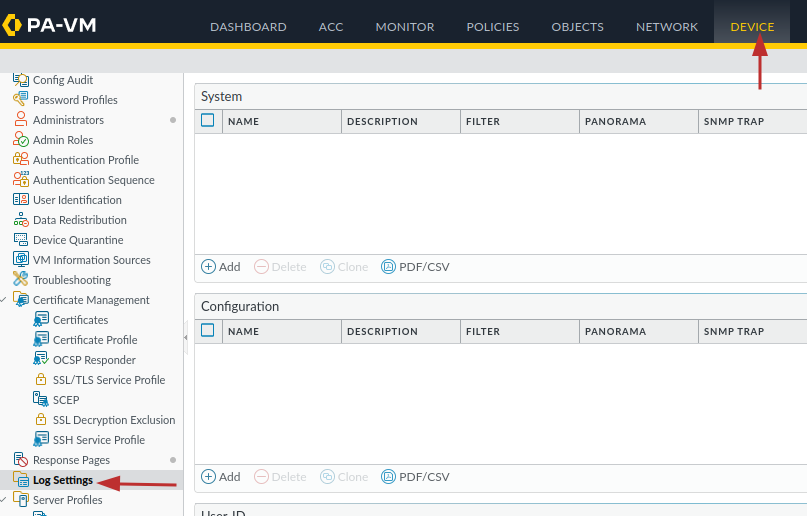
- For each sections in the Log Settings, click on the Add button to bring the configuration screen (System in the screenshot below)
- Provide an appropriate name
- In the Syslog section, click on the Add button and select the previously created Syslog Server Profile named “Splunk“
- Click OK
- You will need to repeat the same steps in order to configure the rest of the section: Configuration, User-ID, HIP Match, GlobalProtect and IP-Tag.
- Your configuration should like the below screenshot
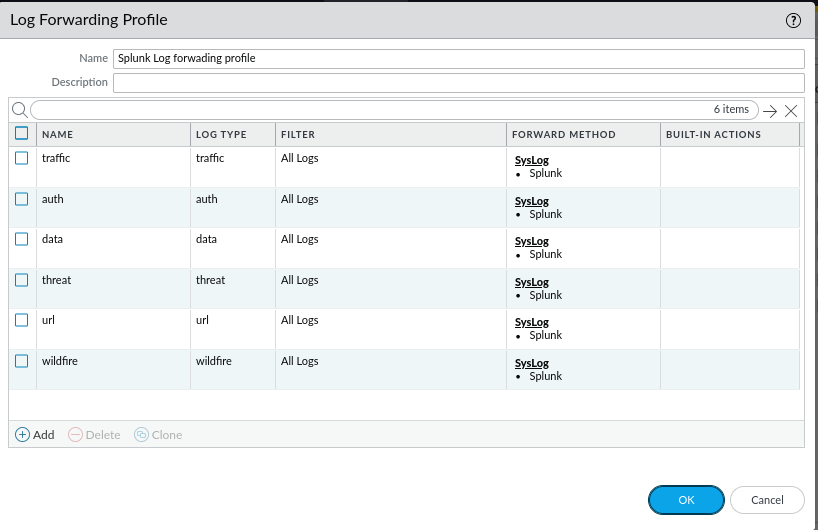
Log Forwarding
- Navigate to Objects -> Log Forwarding
- Click on ADD
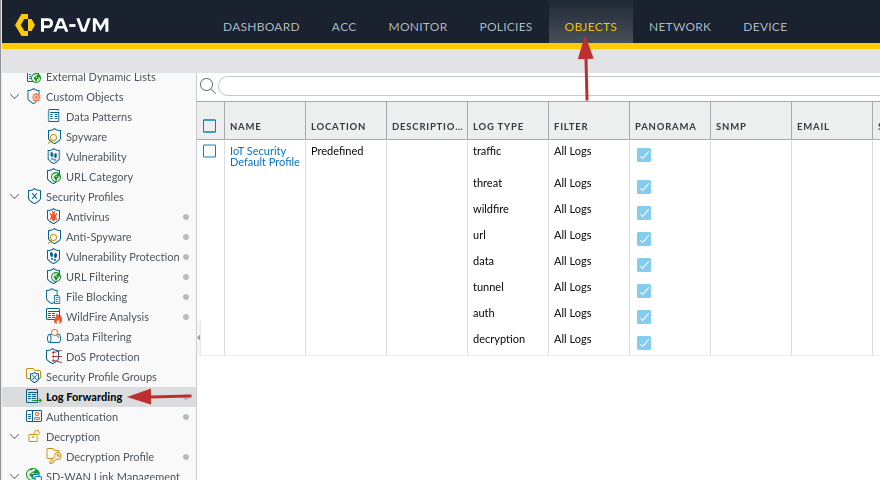
- Provide the appropriate name for the log profile
- Click on add
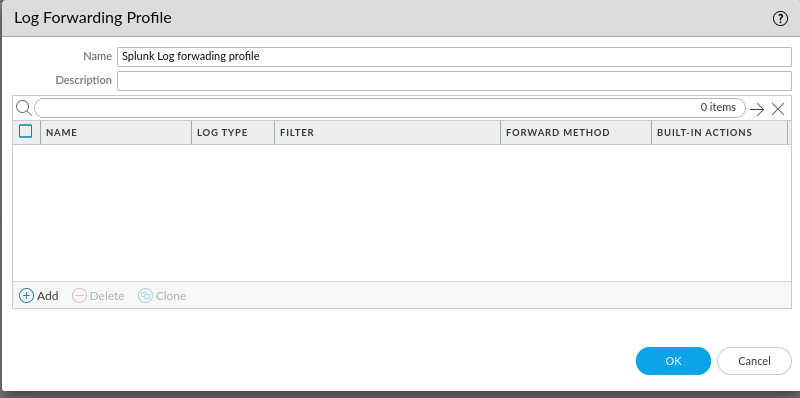
- We now need to select the log type that we would like forward and add it to our profile.
- Click on Add
- Select the appropriate log type
- Add the existing syslog profile
- Click OK
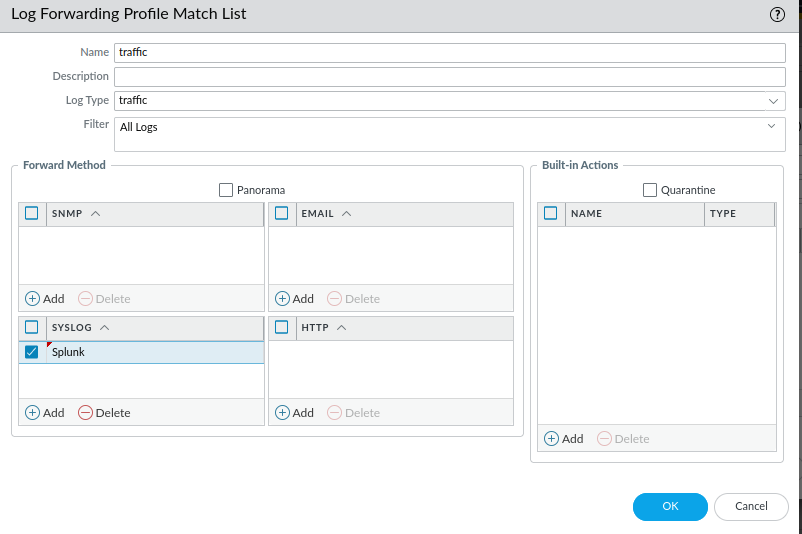
- You will need to repeat the same steps in order to forward other log types such as auth, data, threat, url, wildfire.
- Depending on what log type you selected to forward, your Log Forwarding profile should like the screenshot below
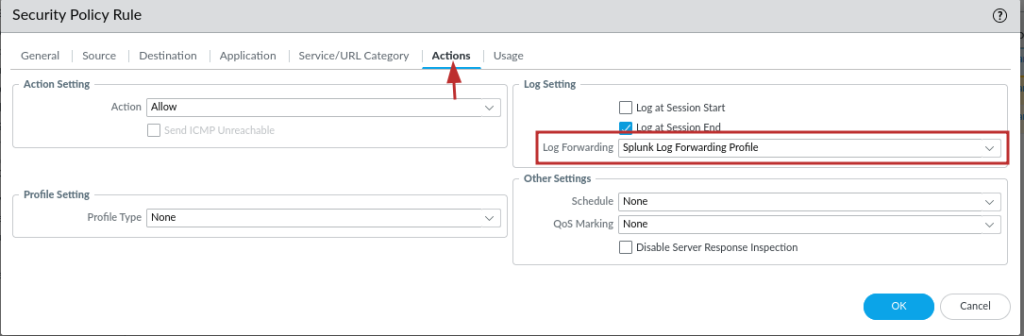
Security Policies
Any existing security policies’ actions will need to be modified by specifying the log forwarding profile we created previously.
- Policies -> Security
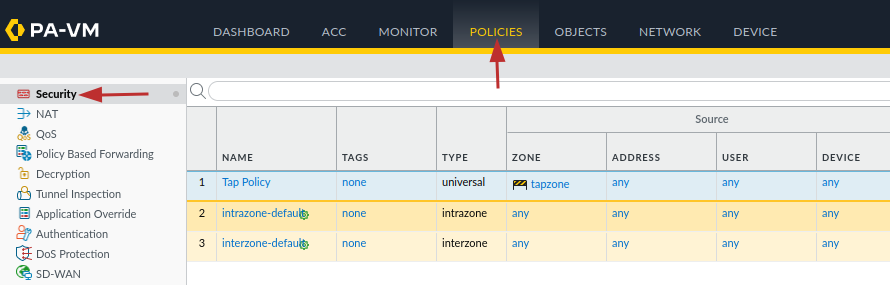
- Select the appropriate policy
- Click on the Actions tab
- Select the previously create Forwarding Profile in the Log Forwarding dropdown menu
- Click OK when done
You can now commit your changes for the changes to take effect.
In the second installment of this series, we’ll delve into validating our configuration to ensure that Splunk is effectively receiving data from our Palo Alto NGFW.
If you have any questions or require assistance, we are actively seeking strategic partnerships and would welcome the opportunity to collaborate. Don’t hesitate to contact us!
